
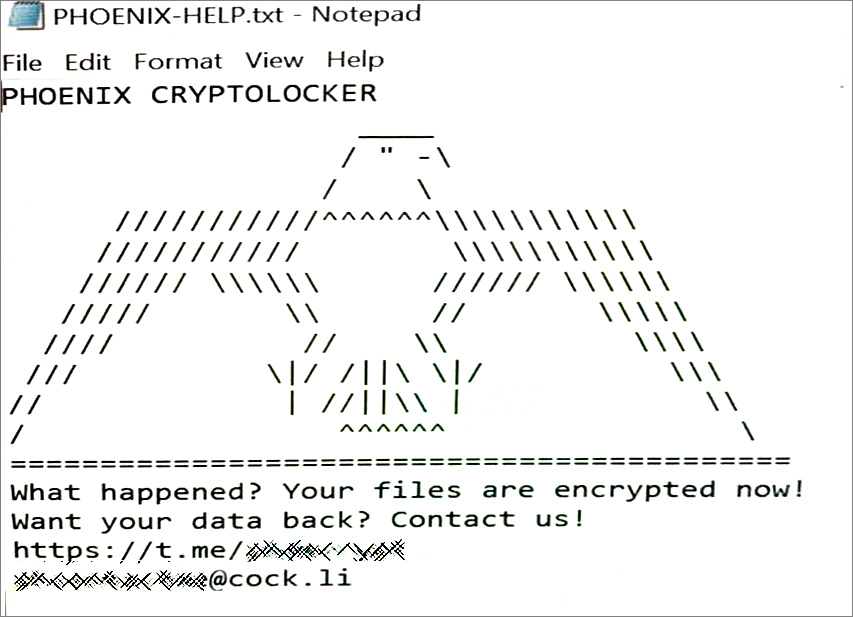
Leading US-based insurance company CNA Financial has fully restored systems following a Phoenix CryptoLocker ransomware attack that disrupted its online services and business operations during late March.
CNA provides a wide range of insurance products, including cyber insurance policies, and is the sixth-largest commercial insurance company in the US according to stats provided by the Insurance Information Institute.
Sources familiar with the ransomware attack told BleepingComputer that the attackers encrypted more than 15,000 devices after deploying ransomware payloads on CNA's network on March 21.
"On March 21, 2021, as previously shared, we detected the ransomware and took immediate action by proactively disconnecting our systems from our network to contain the threat and prevent additional systems from being affected," CNA said in an update published on Wednesday.
BleepingComputer has also learned at the time that Phoenix CryptoLocker operators also encrypted the computers of remote workers logged into the company's VPN during the attack.
Systems are now fully restored
"CNA is fully restored, and we are operating business as usual. Our IT teams and third-party partners have worked hard to restore business operability," the company said on Wednesday.
"We are pleased that in a short time since the ransomware event, we are now operating in a fully restored state."
The insurance firm deployed endpoint detection and monitoring tools on the newly restored systems during the recovery process.
CNA also ensured that the restored systems were not reinfected by scanning them again before bringing them back online.
While investigating the impact on data stored on its systems, the insurance provider did not find any evidence of stolen policyholder info surfacing being exchanged or put up for sale on the dark web or hacking forums.
"We do not believe that the Systems of Record, claims systems, or underwriting systems, where the majority of policyholder data–including policy terms and coverage limits–is stored, were impacted," CNA added.
"Importantly, CNA has been conducting dark web scans and searches for CNA-related information and at this time, we do not have any evidence that data related to this attack is being shared or misused."
Cyber insurance firms are a valuable target
Attacks on companies with cyber insurance policies are very lucrative for ransomware groups as they are more likely to pay the ransom.
However, breaching an insurance provider's network and stealing customers' policy info could be an even more lucrative way to increase their attacks' effectiveness.
With the help of this data, ransomware gangs can easily create a list of insured companies, including their policy limits, to target in the future.
This would also most likely make it possible for ransom demands custom-tailored to each victim's policy coverage.
In a recent interview, the REvil ransomware operation said that hacking insurers' systems helps create lists of possible targets more likely to pay a ransom.
While at this time, it is not yet known if the ransomware group has stolen unencrypted files before encrypting CNA's systems, the company said that it would abide by "notification obligations to policyholders and impacted individuals."
Using double-extortion as a tactic has become commonplace for most active ransomware operations, with victims regularly alerting their customers or employees of possible data breaches following ransomware attacks.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now